
Project
Overview
Purpose:
We address the socio-technical cybersecurity risks of operationalising machine learning models in order to
-
to understand the cognitive processes and user behaviours that impact on the security of MLOps
-
to model these processes and behaviours so that we can securely deliver human-machine teaming in MLOps
-
to understand how to defend MLOps against subversion as well as how to attack the MLOps of adversaries
Motivation

Work package 1
Task 1.1.
The Social Practice of Data Scientists in MLOps:
-
Qualitative analysis of MLOps
-
Identifying how links between different team functions can be vulnerable
Task 1.2.
Developing a Naturalistic Understanding of Analyst Decision Making:
-
Naturalistic Decision Making (NDM) study with analysts who rely on implementations of MLOps through the field work
Security Dialogues: DevSecOps
-
Addressing security as a social practice
-
Creating a peer-to-peer dialogue between software developers and security practitioners
-
Developing a better understanding of risk

Kim, G., Behr, K. and Spafford, K., 2014. The phoenix project: A novel about IT, DevOps, and helping your business win. IT Revolution. Vancouver
Work package 2
Task 2.1
Modelling the Socio-Technical Security Risks of Human-Machine Teaming:
-
comprehensive table of threats with historical probabilities of occurrence;
-
probabilistic future-looking mapping of human-machine teaming using input from WP1 as well as survey data
-
Task 2.2
Developing a Human-Machine Teaming Digital Twin:
-
MLOps Digital Twin Dashboard
Work package 3
Task 3.1
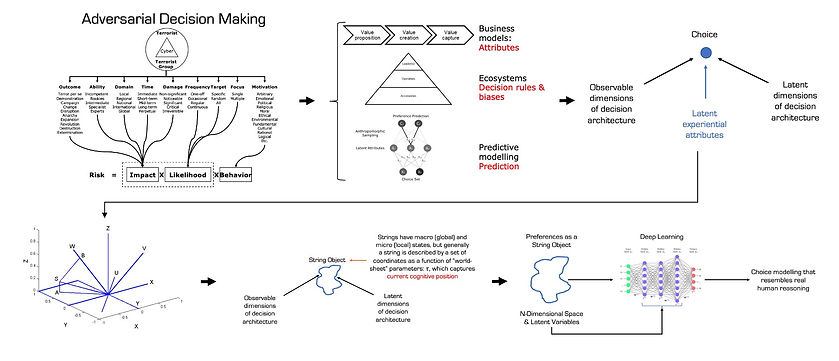
Modelling Strategic Interactions for Benign and Adversarial MLOps:
-
Use game theory to explore how multiple human-machine players on both sides (i.e., in at least 4-player games) interact within and across human-machine teams in games of incomplete information
Task 3.2
Developing Computational Game Theoretic Algorithms for Cyber Deception:
-
Model realistic attack and defence on MLOps

This project
-
contributes to building a cybersecurity research capability between social and behavioural science, data science and computer science;
-
forges a new research partnership between team members and their research institutions;
-
aims to make a significant internationally recognised Australian-based contribution to cybersecurity, machine learning, data science and transdisciplinary research;
-
increases the capability of the national intelligence and security community by developing new practical methods for ensuring the cybersecurity of MLOps;
-
facilitates advances in MLOps that would be of benefit across the intelligence community;
-
aims to enable the national intelligence and security community to participate in the research and to co-design solutions.